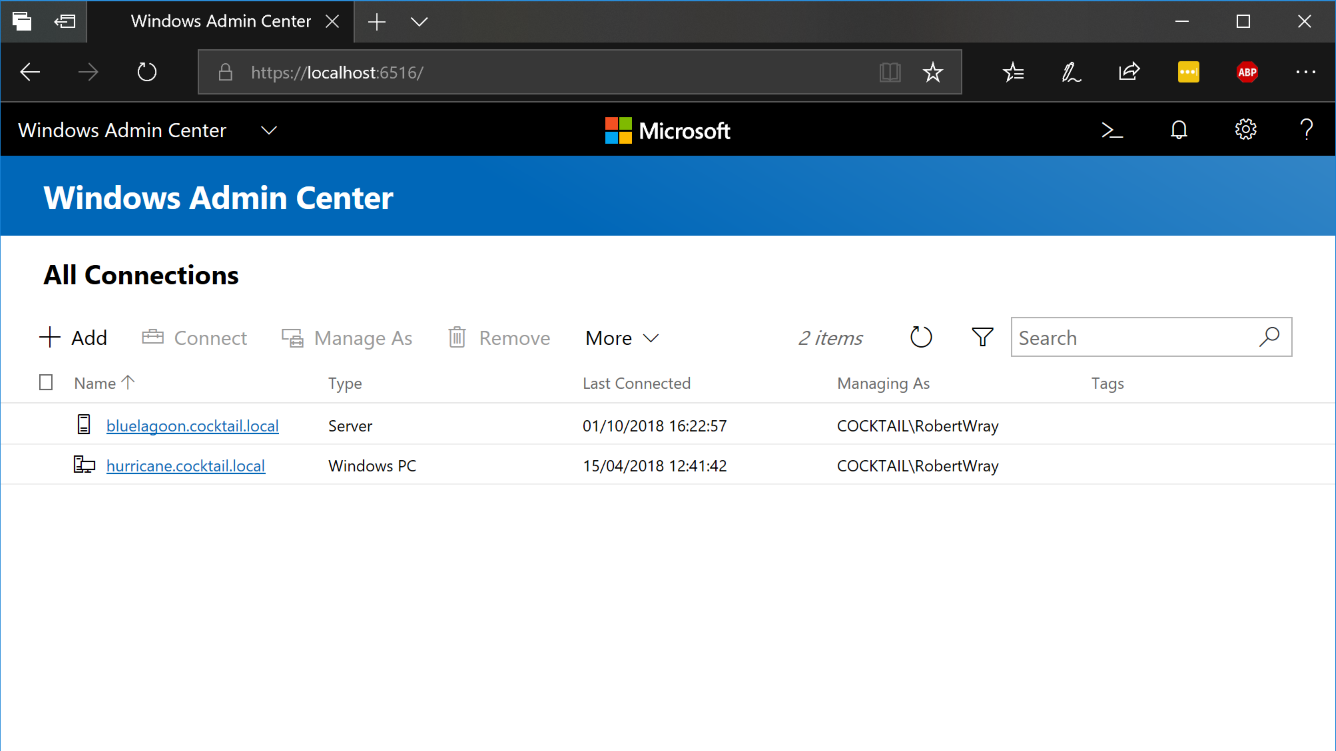
A brief look at the Windows Admin Center (1809)
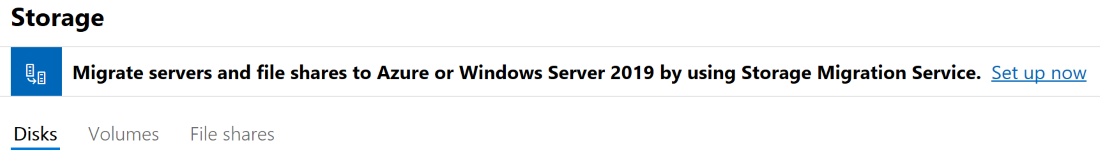
A few days ago I happened to look at the list of recently installed updates in the Settings app and noticed that I'd received an update for Windows Admin Center 1809 which reminded me that I'd installed it quite a while ago to have a look at and hadn't really done so! Originally released by Microsoft in September 2017 under the name Project Honolulu, the WAC provides the ability to view information about a massive number of different parts of Windows (both for client and server OS's) and the ability to change configuration as well. The list of feature areas that can be viewed and configured ranges from installed certificates, through to the Event Log, Registry and Hyper-V VM and Virtual Switch configuration. There are, of course, various places where Microsoft have dropped in hooks (for want of a better way of describing them) to Azure services such as under Storage which shows a top-hat banner:
The place this is perhaps most obvious is when clicking on the Backup option when connected to a server which presents you with the option to Set up Azure Backup and well, not a lot else!
Whilst not as feature rich as the RSAT tools, WAC gives you access to so many areas of configuration for Windows servers and PCs that with a bit of luck it should cover a good number of day-to-day administrative tasks.
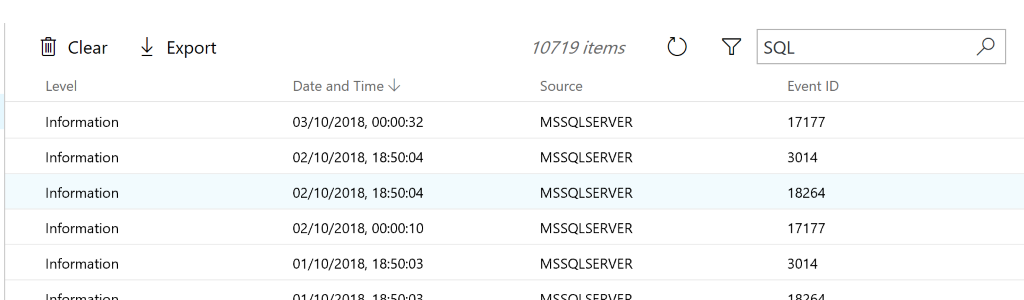
Viewing the Event Log
Perhaps the most compelling feature that I've found so far is the Event Log viewer, or Events as its now called in WAC. Anyone who's worked with Windows devices for a while will be all too familiar with sitting, waiting and watching this screen:
And waiting, and waiting, and waiting some more. Ever since the "classic" Event Viewer was replaced somewhere around the Windows Server 2003 era with the current version, waiting for it to load has become a pastime where it's verging on being that slow that the "go away and make a cup of coffee" running gag almost holds true.
It's quicker to start Windows Admin Center, wait for it to load in your browser, choose your local PC, wait for the UI to populate with the available components on the left-hand side and choose Events and then select Application under Windows Logs than it is to do the comparable set of operations with the built-in Event Viewer. The Search facility is lightning quick as well, though it does appear to be client-side and operating on the list of Event Log entries already retrieved:
Fast and effective, what more could you ask for?
Certificates
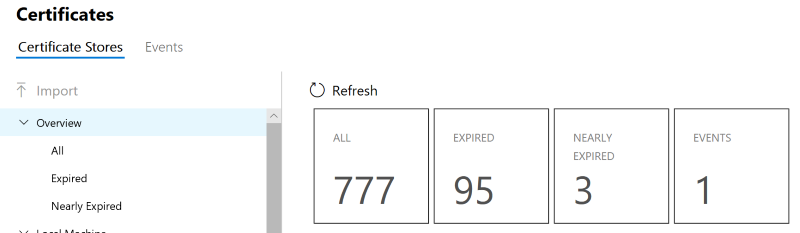
One of the infrequent tasks I have to perform is replacing certificates (I know, I know, Let's Encrypt all the things!) and the WAC user=interface gives a useful summary of the current state of certificates on a server:
The immediately obvious negative to this is that when you click through to Nearly Expired, either by clicking on the tile or the option in the treeview to the left, there's a reasonable chance that you'll see "noise" in the list as I did. All three certificates that were listed as nearly expired had names similar to Microsoft Local Attestation Service which means that there's precisely nothing I can do about them. If this excluded (by default would be nice!) system issued and managed certificates that'd be nice.
One other bit of awesome is the search that appears to be ubiquitous across most areas of WAC, certificates included. The only thing that'd make it better for certificates is if the search spanned all available stores rather than being constrained to either the Current User or Machine store.
Connection Problems?
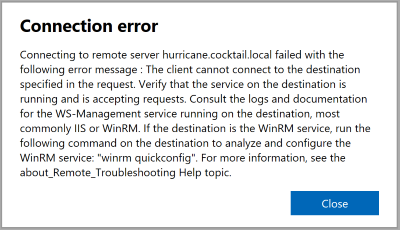
Part way through writing this post I upgraded my Surface Book to Windows 10 1809 (I genuinely have no idea what it's being branded as this time!) which caused WAC to stop being able to connect to it, popping a dialog saying:
For those who're seeing this message, which has the text:
Connecting to remote server hurricane.cocktail.local failed with the following error message : The client cannot connect to the destination specified in the request. Verify that the service on the destination is running and is accepting requests. Consult the logs and documentation for the WS-Management service running on the destination, most commonly IIS or WinRM. If the destination is the WinRM service, run the following command on the destination to analyze and configure the WinRM service: "winrm quickconfig". For more information, see the about_Remote_Troubleshooting Help topic.
The first thing I tried was to read the error message and follow the instructions in there, so opening a command prompt (as Administrator!) and running winrm quickconfig, this gave me a big old wall of text:
C:\WINDOWS\system32>winrm quickconfig
WinRM is not set up to receive requests on this machine.
The following changes must be made:
Start the WinRM service.
Set the WinRM service type to delayed auto start.
Make these changes [y/n]? y
WinRM has been updated to receive requests.
WinRM service type changed successfully.
WinRM service started.
WSManFault
Message
ProviderFault
WSManFault
Message = WinRM firewall exception will not work since one of the network connection types on this machine is set to Public. Change the network connection type to either Domain or Private and try again.
Error number: -2144108183 0x80338169
WinRM firewall exception will not work since one of the network connection types on this machine is set to Public. Change the network connection type to either Domain or Private and try again.
However, wall of text it might be, but it appears it worked! Trying to connect to WAC gave me a credentials prompt via a fly-out from the right-hand side of the screen. Leaving Use my Windows account for this connection selected and clicking on the Connect button didn't seem to work (at least for me) but closing and re-opening my browser cleared whatever had glitched and let me back in!